Empower resilience with the leading critical event management platform
Everbridge High Velocity CEM™, powered by Purpose-built AI


Everbridge named a Leader in The Forrester Wave™: Critical Event Management
Discover why Everbridge was named a Leader in critical event management by Forrester. Their report compares 10 vendors, evaluating platforms based on current offering, strategy, and market presence – where Everbridge scored highest in all three.
Over 6,500 global customers trust Everbridge
An extensive customer base across private and public sectors.
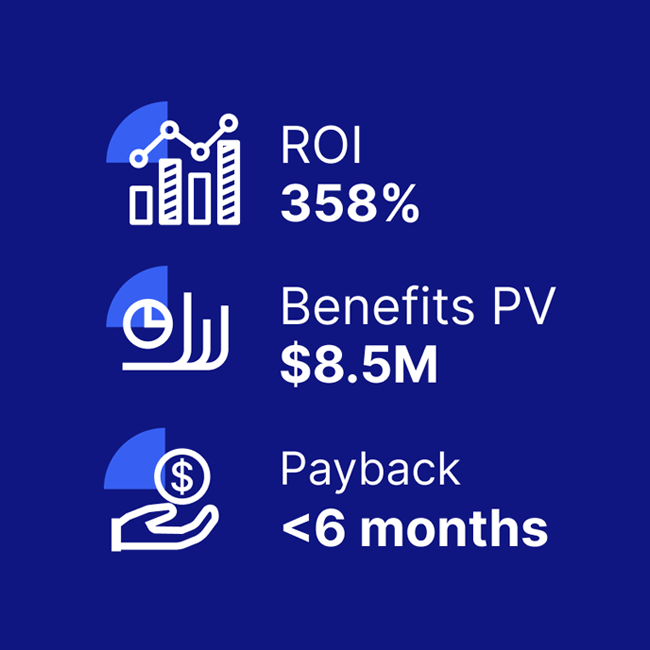
Significant proven ROI
With Everbridge, resilience translates into results. Forrester Consulting revealed that our customers achieve:
- 358% ROI over three years
- $3M in operational efficiency gains
- $2M saved through reduced IT downtime
- $1.5M in productivity improvements for security operations
Discover the value Everbridge can bring to your organization. Access our ROI calculator, checklist, and Total Economic Impact (TEI) study.
Customers love Everbridge
“Everbridge is constantly looking for ways to improve the service offering, based on customer requests and needs.”
Mark T.
“When seconds matter, notify visitors, residents and employees over multiple communication paths, including voice, SMS, email and social media.”
Richard O.
“The reliability of sending notifications and knowing that all recipients will be sent notifications until they acknowledge is reassuring.”
Roger C.
Unified platform for greater resiliency in critical event management
Billions of critical interactions delivered globally every year. Full High Velocity CEM technology platform, powered by Purpose-built AI.
Platform
One platform.
One process.
One response.
Anywhere.
Scale
High Velocity CEM solutions to support teams of all types and sizes, globally.
Data
AI-powered threat scoring and 25,000+ real-time data sources.
Products
AI-powered decision-ready risk intelligence and full lifecycle automation to navigate critical events with confidence.
IP patents
160+ worldwide
patents.
Everbridge provides the most complete, end-to-end suite of solutions for managing physical and digital critical events
Our High Velocity CEM platform, powered by Purpose-built AI, provides the highest levels of actionable risk intelligence in the industry – helping you keep your business better protected.
From physical protection in offices and public spaces, and digital protection while online, to on-the-go solutions to keep your people safe wherever they are, Everbridge is the only critical event platform you need.
Try Everbridge for yourself with a free Risk Intelligence trial.